
By comparison, the brilliant blockchain technology that makes Bitcoin possible has flown under the radar. This isn’t surprising given the sophistication involved and our tendency to avoid thinking hard, particularly when understanding something doesn’t seem necessary.
Here’s the thing though: blockchain technology is so well suited to the future that it will become a feature in our lives whether we understand it or not. Like any transformative technology, those who get to grips with it will enjoy a richer worldview replete with more opportunity.
At the very least, understanding how a blockchain works will give those who invest in cryptocurrencies a fundamental grounding in the asset class rather than one based on speculation.
Crime of the future
Cybercrime can take many shapes but in most cases the mechanics are quite simple:
By 2030, it’s estimated that there’ll be roughly 25 billion devices connected to the internet. At the same time, we are producing unfathomable amounts of data, a portion of which will be sensitive. And it’s very difficult to catch cybercriminals, especially when they operate in anti-West domains. These three factors are behind the tangible and entrenched acceleration in global cybercrime.
The daunting thing about cyberattacks is that the perpetrators are just as crafty as the programmers developing cybersecurity systems. Human gullibility is also infamous in undermining the latter, evidenced by the continued use and effectiveness of simple email phishing scams.
If there’s one thing that blockchains are good at, it’s protecting data from bad actors. To see why, let’s start by exploring the first half on the noun.
What’s in a block?
One of the key attractions of bitcoin is that it’s very difficult to steal compared to the cash you keep in your wallet or bank account. If you can understand why that’s the case, then you can understand how blockchain technology can be used to protect data. A (bit)coin, after all, is just data.
A ‘block’ is where the data is stored. Every block has two parts. The first is the ‘block header’ which contains the following information (don’t panic, we’ll makes sense of these terms as we go):
The second part of the block contains bitcoin transaction data i.e., records of how bitcoins are changing hands. Each block in the Bitcoin blockchain can only hold 1MB of data, equal to roughly 500 bitcoin transactions. When that space is exhausted, a new block is needed. To understand how new blocks are created, we need to grasp the concept of ‘hashing’.
Know your hash
A hash is simply a number that is generated by an algorithm given certain inputs. There are many different ‘hashing’ algorithms, each producing a hash of a certain, fixed length. The Bitcoin blockchain uses the SHA-256 iteration.
Here’s an example of how an input is transformed into a hash:
Input: Sasfin Wealth
Hash: da81f03e238851220e9967ddbee1de15a6936d76229a2ce8359ad78b22b78822
The hashing algorithm has essentially encrypted ‘Sasfin Wealth’ into a number. Note that the hash is represented in a hexadecimal format which includes letters, but you are looking at a number. Change just one character in the input (Sasfin We@lth, for example) and the hash generated will be completely different. You can try hashing out for yourself here.
In the context of the Bitcoin blockchain, hashing is used in two ways:
First, pairs of new Bitcoin transactions are hashed together repeatedly until they are bundled up inside one hash, known as the Merkle root. Think of the Merkle root as an encrypted summary of all the transactions in the block.
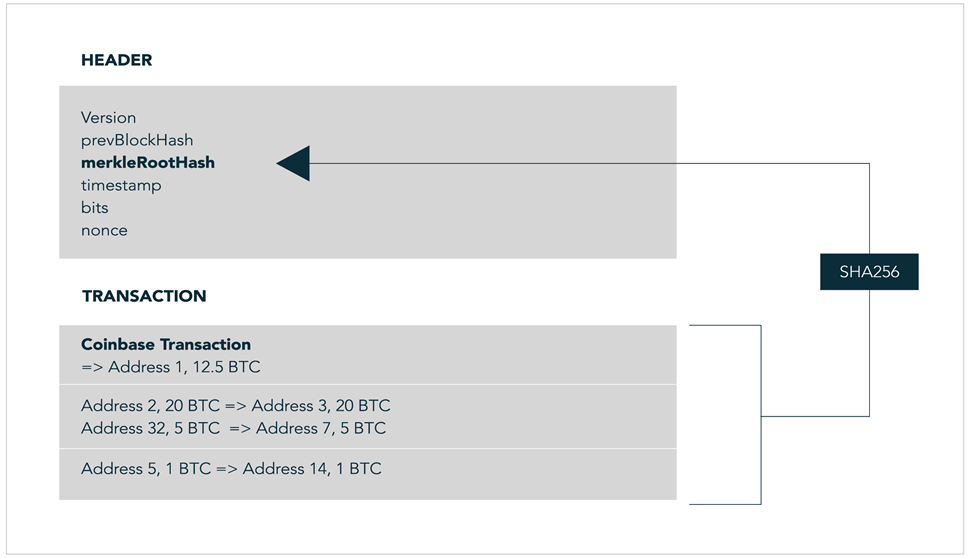
Second, all the data inside the block header (visible above) is hashed twice through the same SHA-256 algorithm to generate the block’s ‘header hash’.
Here comes the crux of the matter: that header hash needs to satisfy a demanding criterion for the new block to be valid. If it doesn’t, it won’t be accepted into the chain, and a new header hash must be generated and tried. This iterative process is known as ‘mining’.
How does mining work?
What is that demanding criterion? Simple: the numeric value of the generated header hash must fall below a threshold called the ‘target hash’ (or bits).
One of the quirks of the Bitcoin blockchain is that the time between creating new blocks is set at 10 minutes. That rule is enforced by the target hash. At the inception of the Bitcoin blockchain, its numerical value would have been high, making it relatively easy to generate a valid header hash below it.
But as more miners enter the fray, the target hash is adjusted lower. This adjustment is made every 2,016 blocks, which equates to roughly every two weeks. A lower target hash makes it more unlikely that a randomly generated header hash will fall below it. In this way, more computing power is offset by a lower target hash to keep block creation set at 10-minute intervals.
At today’s target hash, the chance that a given header hash falls below it is about:
= 0.00000000000000000002%.
To improve their odds, miners hash the block header repeatedly until they (or someone else) find a valid header hash for the block. Of course, if you hash together the same inputs, you’ll get the same header hash.
Here’s where the nonce and timestamp come in – they can be varied. The nonce has 4 billion possible values while the timestamp can be changed every second. The more computing power a miner has, the faster they can rehash the block header, varying the nonce and timestamp, and the more header hashes they’ll generate.
When the miner finds a valid header hash below the target hash, they are said to have found the ‘golden nonce’.
There’s a lot to take in here. But the result is that a new block is created to house fresh, encrypted bitcoin transactions. Importantly, the block’s header hash contains the previous block’s header hash, linking the two blocks together. Those links create an unbreakable chain.
Before the new block is added to the blockchain a final security hurdle must be cleared. It’s called ‘consensus’ and it’s what makes blockchain technology so good at protecting data.
Safety in numbers
The Bitcoin blockchain is essentially a ledger is which all bitcoin transactions are recorded. But unlike a physical ledger, or a digital one controlled by a single entity, this ledger is available to anyone who wants it.
Those who download and store the full blockchain ledger on their computers are known as ‘nodes.’ They have a vested interest in making sure every transaction is legitimate.
When a miner generates a header hash below the target hash, that block is sent to every node in the Bitcoin blockchain network. For it to be added to the chain, more than 50% of the nodes must validate the block – i.e., consensus. Why is this check so powerful?
Here’s the gist of it: if a hacker tries to commandeer bitcoin by manipulating transaction data in a block, the transaction hashes would change, which would change the Merkle root, which would change the header hash, which would throw the block out of sync with the rest of the chain.
Nodes, who run a series of validation checks on new blocks, would notice the anomaly and ignore the block, rendering it invalid. The incumbent transactions would therefore not be confirmed, and the nefarious would-be bitcoin owners would not be able to spend them. In short, blockchain technology harnesses a well-meaning crowd to thwart individual bad actors.
Wouldn’t you want your financial, medical, or sensitive business information to be stored like bitcoin transaction data? With cybercrime on the march, data can turn to the blockchain for protection.